by Sue Halpern
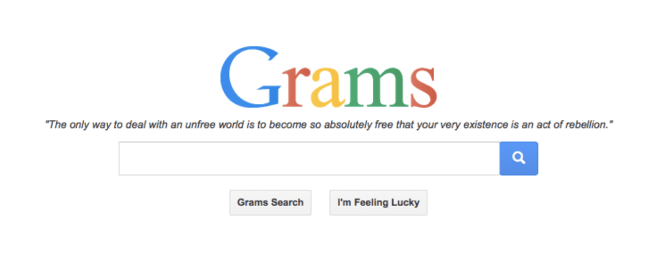
It turns out the NSA’s ICREACH search engine, the one that may be sharing the intimate details of your life among a thousand analysts, isn’t the only secret, Google-inspired search engine out there. Say you’re interested in buying some of those credit card numbers that Russian hackers are so good at lifting from American banks like J.P. Morgan. Or some meth or heroin or the services of a hitman. All these things have long been available through the Internet’s “darknet,” but tricky to get at. They become much more accessible with the “GRAMS” search engine, which looks just like Google (and ICREACH) (why mess with a winner?), and works essentially the same way. Type in the word “weed” and you will be offered 5 grams of Santa Maria weed from a vendor in Germany, a pound of “chronic outdoor low grade” weed from a seller in the United States, and so on. Type in the word “handguns,” and the first two listings are for “The Terrorist Handbook” and “The Terrorist Encyclopedia” which are all about making explosives from various substances available at the hardware store. The third listing is for the latest CAD files for making 3D printed guns. Like eBay, each listing has a link for other items in the vendor’s virtual store and comments from buyers:
Stars Review Freshness ok 1 day ago Exceptional 1 day ago Perfect, thanks ! 1 day ago Great feedback! Recommend 1 day ago got wat i paid for 1 day ago Everything ok – honest seller as expected! Thanks! 1 day ago Good service fast delivery. 1 day ago Thanks mate. Great product! 1 day ago
To get to GRAMS, and to the Darknet more generally, you have to go through Tor, the anonymizing browser developed by the US Naval Research Laboratory, which is now an open source project. Because Tor hands off each message in pieces to many different relays–there are 3000 in all–it makes those messages very difficult to trace and to read in transit. As a consequence, TOR has been useful for journalists needing to shield a source, or dissidents working against oppressive regimes, or victims of domestic violence, or ordinary people concerned with government overreach. It’s also been very good for cyber criminals, drug dealers and pedophiles.
You might expect that Tor traffic would be fertile ground for NSA spying, and it would be if it could crack the encryption and de-anonymize users, but it’s been challenging. One of the NSA documents leaked by Edward Snowden was called “Tor Stinks,” and detailed all the mostly failed attempts to get into Tor. But since the Snowden leaks, there have been lots of speculation about the NSA’s growing abilities to crack it. On July 4th, when Tor administrators warned users that the service had been breached, fingers didn’t point at the government directly, but at a group of computer scientists at a Carnegie-Mellon lab funded by the government. From the July 31 WSJ:
In a blog post, Tor said outsiders “affected” some users in the first half of the year.
“Unfortunately, it’s still unclear what ‘affected’ includes,” the post said. “While we don’t know when they started doing the attack, users who operated or accessed hidden services from early February through July 4 should assume they were affected.”
Users who act as Tor relays, or hop points, should update their software, the group said. At the Black Hat hacker conference in Las Vegas next week, the Carnegie-Mellon researchers planned to demonstrate a hack that allowed them to unmask some Tor users. They relied on techniques similar to the tactics unveiled by Tor on Wednesday. Lawyers for the university cancelled the talk last week.
Fast-forward to earlier this week when former Health and Human Services employee Timothy DeFoggi was convicted on child pornography charges after a lengthy investigation by the FBI, which had broken into a darknet website run by a man in Nebraska named Aaron McGrath:
The FBI installed malware remotely on the machines of visitors of McGrath’s websites which could identify computers’ IP addresses, as well as its MAC addresses, directly identifying PCs’ networking cards, and other identifying data.
The malware and other FBI techniques “successfully revealed the true IP addresses of approximately 25 domestic users who accessed the sites (a small handful of domestic suspects were identified through other means, and numerous foreign-based suspect IPs were also identified)”, prosecutors wrote in a court document.
DeFoggi, like many pedophiles, thought he was safe from view because McGrath’s site, “Pedobard,” was run through Tor. DeFoggi’s job at HHS? Chief of Cybersecurity.